If you are looking for Fallout 4 F4SE failing to start – Fallout 4 Technical Support – LoversLab you’ve visit to the right place. We have 35 Images about Fallout 4 F4SE failing to start – Fallout 4 Technical Support – LoversLab like Fallout 4 — Расширенная среда анимаций (AAF) / Advanced Animation, Fallout 4: F4SE – Updates, Help and Download – Guide and Tips and also In AAF, what is AV? – Fallout 4 Technical Support – LoversLab. Read more:
Table of Contents
Fallout 4 F4SE Failing To Start – Fallout 4 Technical Support – LoversLab
www.loverslab.com
AAF – Basic Animations Theme At Fallout 4 Nexus – Mods And Community

www.nexusmods.com
aaf fallout loverslab mods animations basic pages theme use fallout4 bed downloads
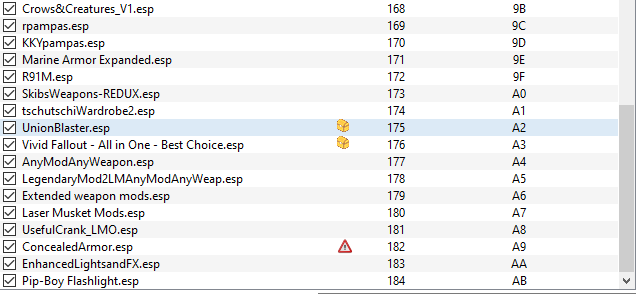
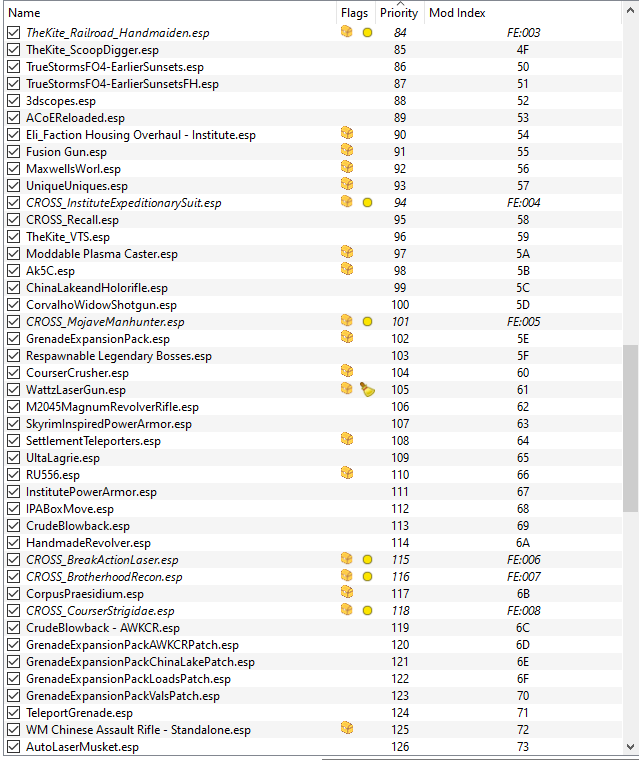
AAF Won't Load. – Page 4 – Fallout 4 Technical Support – LoversLab
www.loverslab.com
In AAF, What Is AV? – Fallout 4 Technical Support – LoversLab
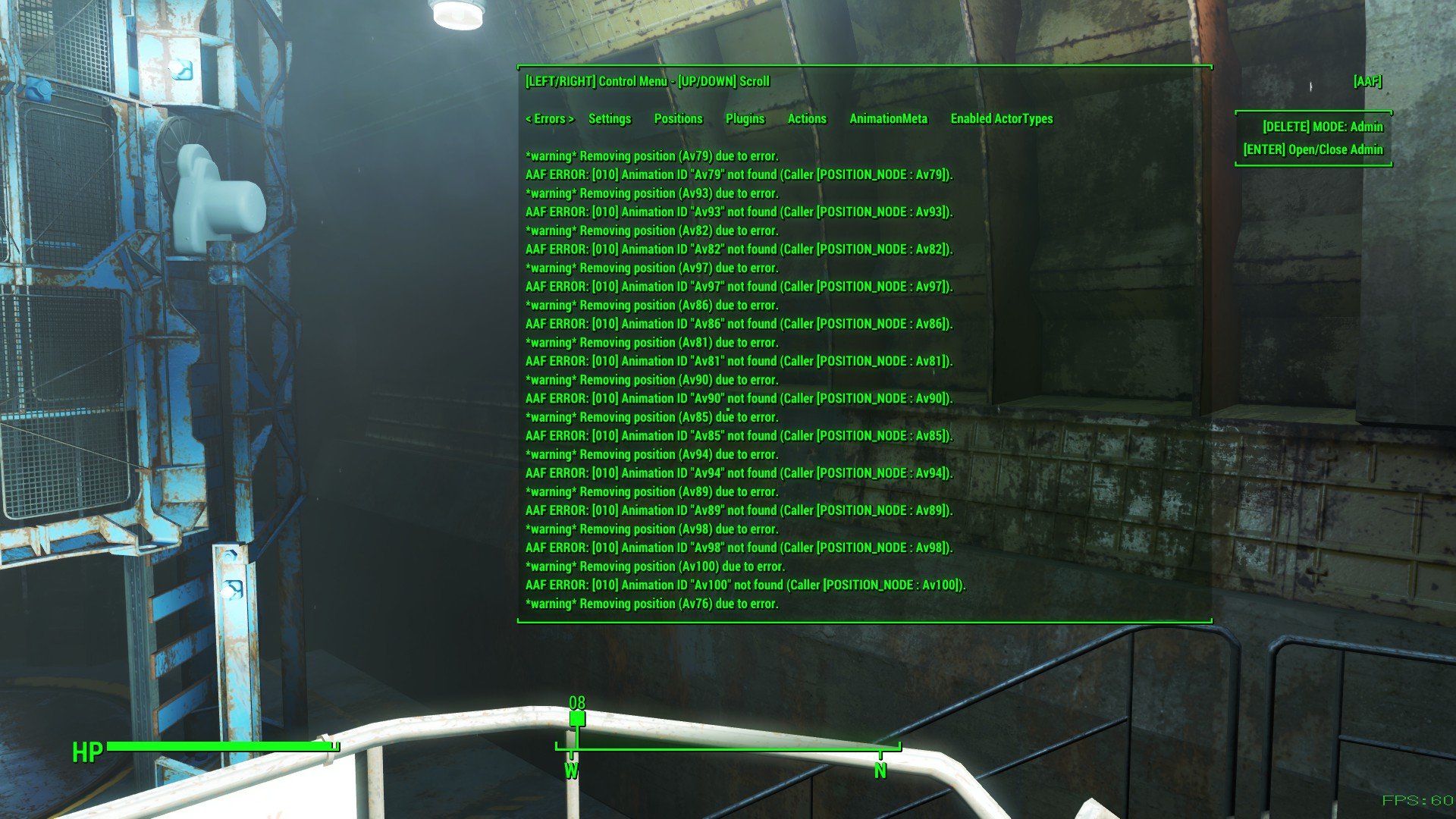
www.loverslab.com
aaf loverslab fallout pop
Fallout 4: How To Install F4SE – YouTube

www.youtube.com
【Fallout 4】「F4SE(Fallout 4 Script Extender)」の導入方法 【+Mod Organizer 2から起動
pcmodgamer.com
No Esp, No Problem: Transform Your Fallout 4 World With These Game

www.youtube.com
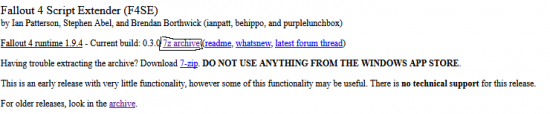
Fallout 4: F4SE – Updates, Help And Download – Guide And Tips

gamescrack.org
f4se fallout gamescrack
Fallout 4 F4SE Failing To Start – Fallout 4 Technical Support – LoversLab
www.loverslab.com
AAF Is Not Showing Up In The Mod Menu, In The Game Itself – Fallout 4
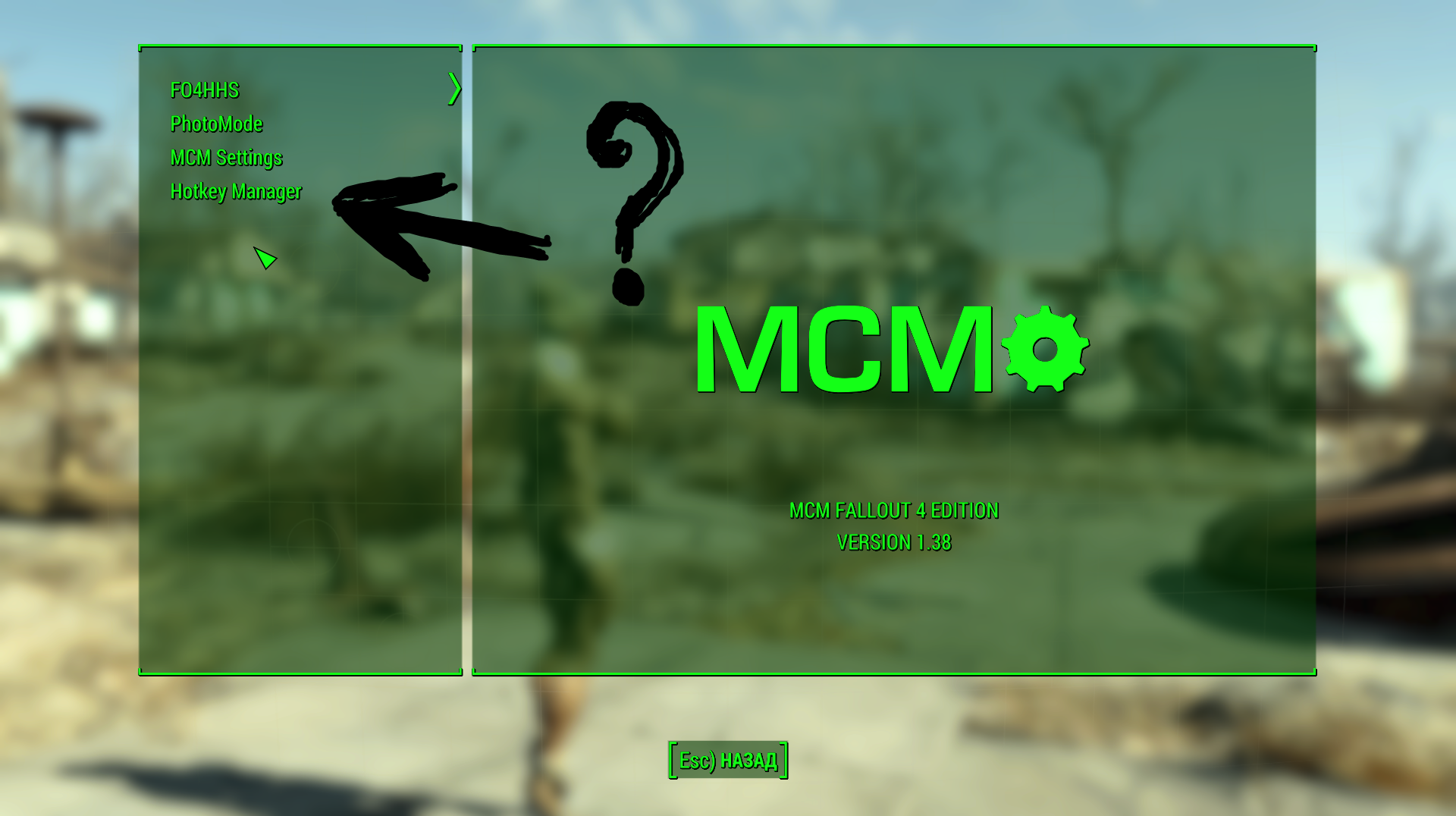
www.loverslab.com
Fallout 4 Place Everywhere Mod & F4SE Setup – YouTube

www.youtube.com
f4se
Fallout 4: F4SE – Updates, Help And Download – Guide And Tips
gamescrack.org
f4se fallout help updated gamescrack
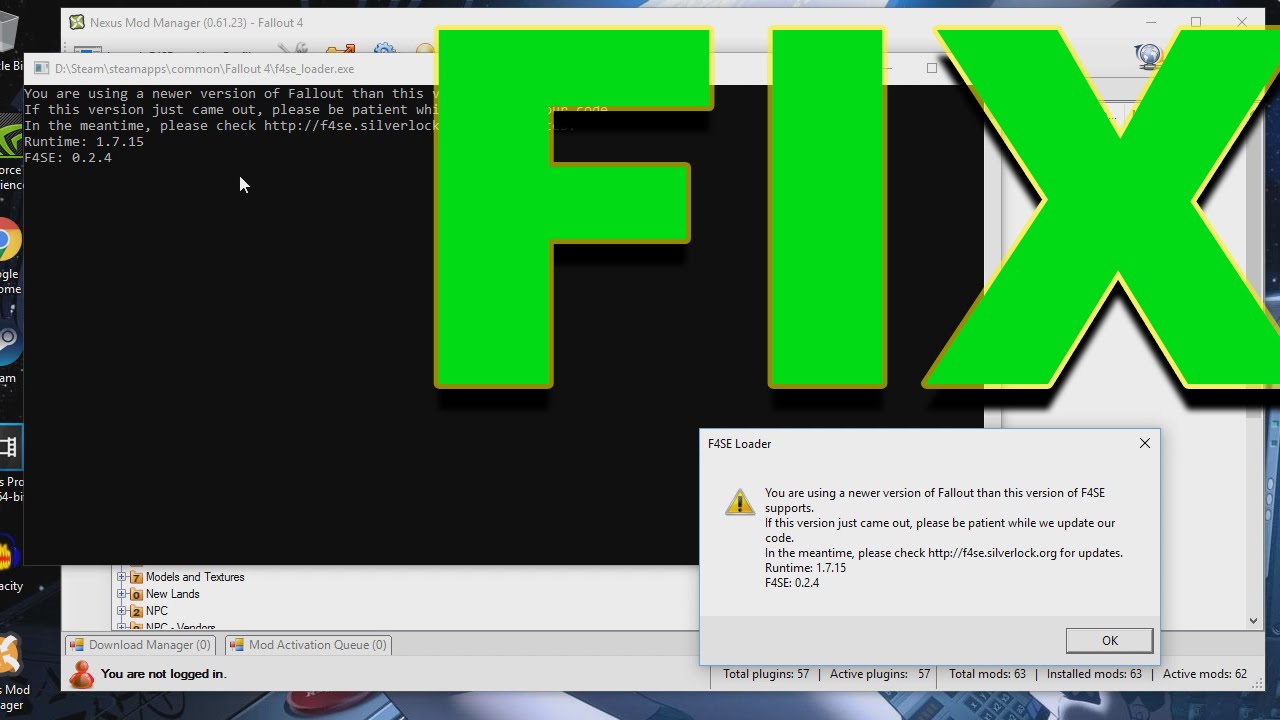
Arreglar Fallout 4 Script Extender F4SE Que No Funciona – R Marketing

rmarketingdigital.com
fallout f4se extender script arreglar
Fallout 4: F4SE – Updates, Help And Download – Guide And Tips

gamescrack.org
f4se fallout gamescrack
How To Fix Fallout 4 Script Extender/F4SE Not Working – MiniTool
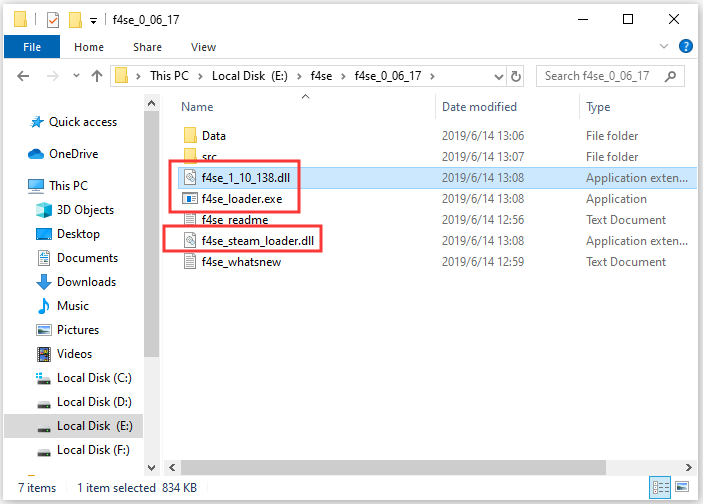
www.partitionwizard.com
f4se fallout extender loader exe copied manager
FALLOUT 4 #9 – F4SE SCRIPT – COMO INSTALAR 2020 – YouTube

www.youtube.com
fallout f4se
☢️Fallout 4 Beginning F4SE, LOOT, FO4Edit, BodySlideStudio (avagy

www.youtube.com
[Archived] F4SE : Fallout 4 Script Extender [Update Linked] – YouTube
![[Archived] F4SE : Fallout 4 Script Extender [Update Linked] - YouTube](https://i.ytimg.com/vi/EdavUN4QghQ/maxresdefault.jpg)
www.youtube.com
Cómo Instalar Fallout 4 Script Extender (F4SE) – YouTube
www.youtube.com
extender fallout script
Fallout 4 Tutorial F4SE+ENB (ITA) – YouTube

www.youtube.com
f4se
AAF Won't Load. – Fallout 4 Technical Support – LoversLab

www.loverslab.com
aaf load fallout loverslab f4se won technical open
Fallout 4 — Расширенная среда анимаций (AAF) / Advanced Animation

gig-life.ru
Fallout 4 Aaf How To Check Error – Hana-Oliver

hana-oliver.blogspot.com
How To Install F4SE (Fallout 4 Script Extender) : FalloutMods

www.reddit.com
fallout extender script
How To Install F4SE For Fallout 4 (2020) – Script Extender V0.6.20

www.youtube.com
f4se fallout extender
Steam Community :: Guide :: Fallout 4 F4SE Installation For Hardcore
steamcommunity.com
f4se fallout steam modding installation hardcore updates manual
F4SE Not Working: Fix Fallout 4 Script Extender Not Working
internettablettalk.com
F4SE Not Working On Fallout 4 [Fixed] – Techisours
![F4SE not working on Fallout 4 [Fixed] - Techisours](https://techisours.com/wp-content/uploads/2020/02/intro-1-300x158.jpg)
techisours.com
f4se fixed techisours
[Fixed] My Game Works Without F4SE, But If I Try To Run FASE I Get CTD
![[Fixed] My game works without F4SE, but if I try to run FASE I get CTD](https://static.loverslab.com/uploads/monthly_2019_12/20191210145034_1.thumb.jpg.b6bbda40d816afc363907ebfb722dc5f.jpg)
www.loverslab.com
-FIX- Fallout 4 F4SE Runtime 1.7.22 UPDATED FIX (Links In Description
www.youtube.com
f4se fallout
How To Install F4SE 2022 | Fallout 4 Script Extender | – YouTube

www.youtube.com
How To Fix Fallout 4 Script Extender Or F4SE Not Working – IR Cache

www.ircache.net
f4se extender ircache
AAF Won't Load. – Fallout 4 Technical Support – LoversLab
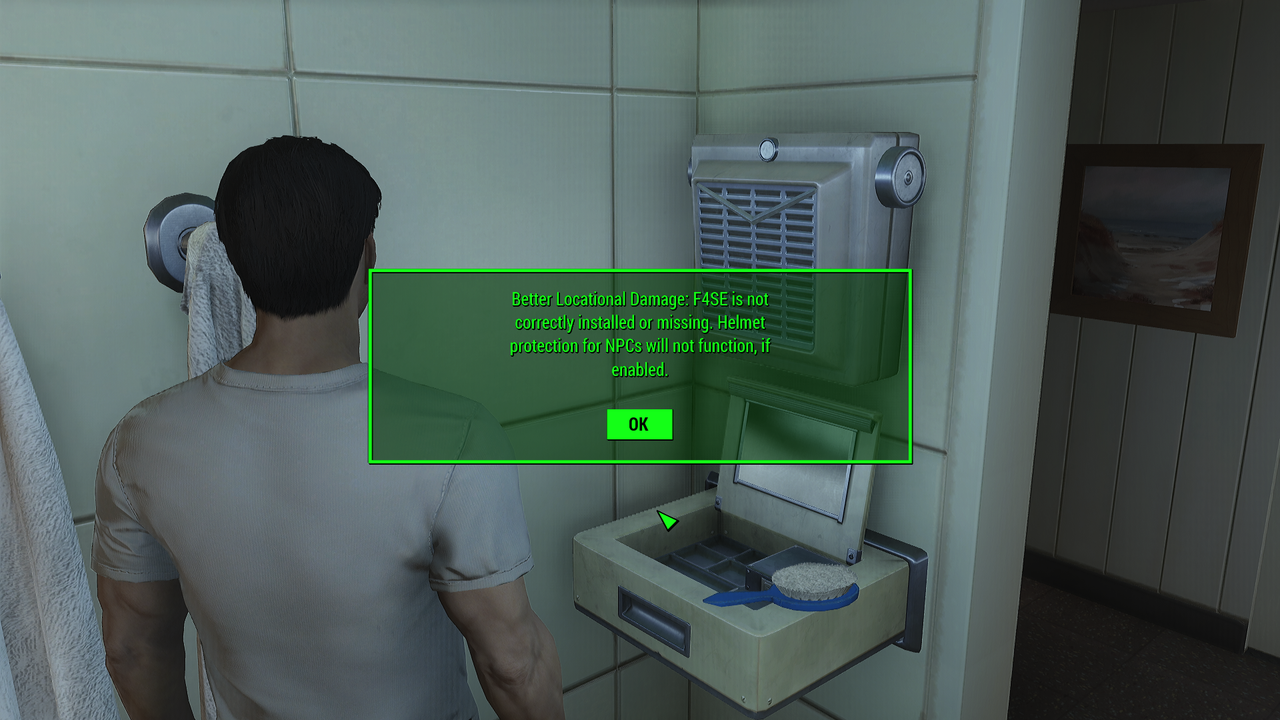
www.loverslab.com
aaf fallout
Debug Messages, After The Installation Of The AAF (Fallout 4)

sharehub.pro
fallout aaf debug installation messages after
Since A Fallout 4 Update In The Last Days This Error-message Always

www.reddit.com
Aaf fallout loverslab mods animations basic pages theme use fallout4 bed downloads. -fix- fallout 4 f4se runtime 1.7.22 updated fix (links in description. Aaf won't load.
 ataylormadelife.com ataylormadelife.com adalah website berita yang memberikan informasi seputar teknologii dan games
ataylormadelife.com ataylormadelife.com adalah website berita yang memberikan informasi seputar teknologii dan games